Are you looking for a secure and reliable way to access websites? Then “/trojyjlcjj8” could be the perfect solution for you. This unique URL string is designed to provide users with a secure and efficient way to access websites, and in this article, we’ll look at what it is, the benefits of using it, how to set it up and use it, troubleshooting tips, and more. So read on for everything you need to know about /trojyjlcjj8
/trojyjlcjj8 is a unique URL string developed to enable secure access to websites. It provides an extra layer of security to protect confidential data and user information from potential hackers. The “/trojyjlcjj8” URL string is encrypted, meaning it can only be decoded by authorized personnel. This helps ensure that only those with the necessary access can view or use the website or section of the website.
In addition, “/trojyjlcjj8” has also been referred to as a “digital key” due to its ability to lock down sensitive data and restrict access to certain websites or sections of a website. This makes it incredibly difficult for hackers and other malicious actors to infiltrate secure systems and gain access to private information.
Having such a secure means of accessing websites offers numerous benefits. For instance, it allows businesses and organizations to make sure their data remains protected, while also offering peace of mind that only those who are allowed will be able see restricted sections of their sites. Additionally, by using “/trojyjlcjj8”, customers can feel confident that their personal information is safe when they visit certain sites.
Overall, “/trojyjlcjj8” is an innovative way for companies and individuals alike to keep their data safe from unwelcome intruders while providing easy access for authorized personnel; making it a valuable tool in any organization’s cybersecurity arsenal.

Benefits of “/trojyjlcjj8
Accessing websites securely has never been easier with the introduction of “/trojyjlcjj8”, a powerful tool that eliminates the need for hardware or software installation, while simultaneously providing an extra layer of protection against potential hackers.
The convenience offered by this URL-based authentication system is one of its major advantages; users can access secure websites from any device with an internet connection without having to download extra programs or applications. This makes it particularly useful for businesses as it allows them to quickly and easily reach their customers without compromising on security.
In addition to its ease of use, “/trojyjlcjj8” also provides high levels of protection due to its encrypted URL strings which can only be decoded by authorized personnel. This ensures that customers are protected from data breaches and their personal information remains safe when browsing certain sites.
For those who require more flexibility in how they protect their data and customer information, “/trojyjlcjj8” is highly customizable according to file types, devices used and user preferences. Additionally, this unique URL string supports a wide range of file types including PDFs and Word documents so that businesses can meet their needs regardless of format type.
How to Use “/trojyjlcjj8
Installing “/trojyjlcjj8” is a straightforward process that requires minimal effort. With this technology, users are able to securely access websites, files, and other sensitive data with ease. To get started, three basic steps must be followed:
- Configuring the URL string: The first step is setting up the “/trojyjlcjj8” URL string by entering in a unique “key” into the system. This key will be used to verify access through authentication methods such as multi-factor authentication or biometrics.
- Verifying Access: After the URL string has been configured, it’s essential to validate user credentials by confirming their identity with additional security measures before granting them access to any sensitive data stored within the site or file they wish to view.
- Accessing Data: Once access has been authorized and verified, users can click on the link in their browser window in order to begin accessing data stored on the website or file connected with “/trojyjlcjj8”. Depending on your security settings, further authentication may be required before users can gain full entry into the site or view any files saved there.
Depending on their use case and requirements for security measures, different types of /trojyjlcjj8 exist – from those intended for corporate environments which often require more robust protection than personal ones do – all of which come with specific installation and setup instructions as well as best practices for achieving optimal performance while remaining secure against potential attack vectors. To maintain systems at peak performance levels throughout regular use, regular maintenance should be performed alongside troubleshooting activities aimed at identifying and resolving any issues that might arise over time before they become major problems down the line.
Ultimately, readers should always have an actionable takeaway when reading about this technology – whether it’s providing advice on how install it properly or sharing tips on how best to maintain its security over time – so that readers feel like they have gained something from reading your post!

Troubleshooting and FAQs
When using “/trojyjlcjj8” to access data, there are a few common issues that may arise. If you encounter any of the following errors, it is important to know how to troubleshoot them quickly and effectively.
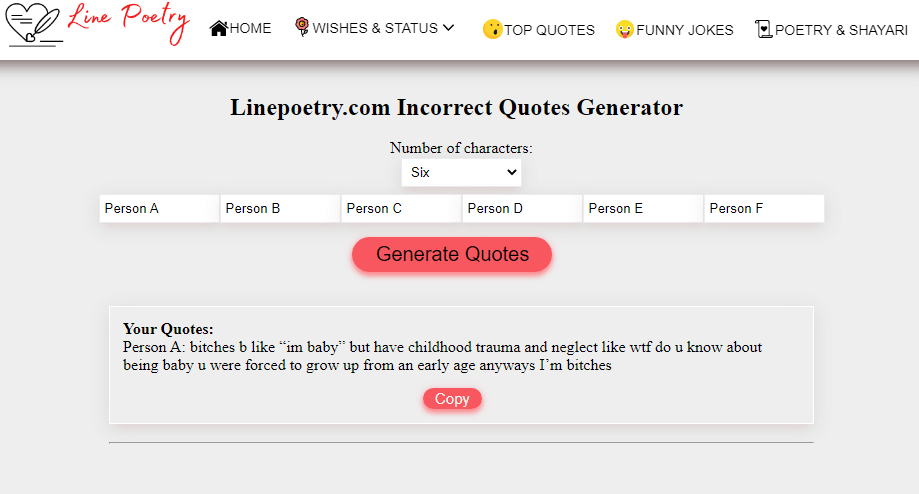
One of the most common issues is an incorrect URL string. To ensure that you are using the correct URL string, double-check the address and make sure it matches exactly with what was provided. If it doesn’t, generate a new URL string and use this instead.
Another common issue is compatibility problems. When accessing websites through “/trojyjlcjj8”, make sure your device is compatible with the software or hardware being used on the other end. Furthermore, if you experience any issues with downloading files or applications, check for any compatibility warnings or notices before downloading them.
For those who require additional help when installing “/trojyjlcjj8”, there are installation guides available online for free which provide step-by-step instructions for setting up the program on different devices and browsers. By following these guides carefully, anyone can successfully install “/trojyjlcjj8” on their system in no time at all!
Finally, if you have any questions about using “/trojyjlcjj8” that aren’t covered in this article or in the installation guide, contact our customer service team who will be happy to help you get set up without any hassle!
By understanding how to troubleshoot potential errors and having access to installation guides as well as customer service support when needed, users of “/trojyjlcjj8” can rest assured that they will be able to securely access websites without fear of encountering difficulties along the way!
In summary, /trojyjlcjj8 is a unique URL string developed to enable secure access to websites. With its encryption capabilities and customizable features, it provides organizations with an invaluable tool for protecting confidential data from potential hackers. Setting up and using “/trojyjlcjj8” is easy and straightforward, but if you encounter any issues there are plenty of troubleshooting resources available.